Forensic Examination of Computers
Computer Forensics
Computer Forensic Investigation, Digitpol provides forensic services to recover forensic data from computers, portable devices and hard disk drives. We can recover deleted data, Internet history, emails, photos and a wide range of services related to recovery of data from Hard Disk Drives and Solid State Drives.
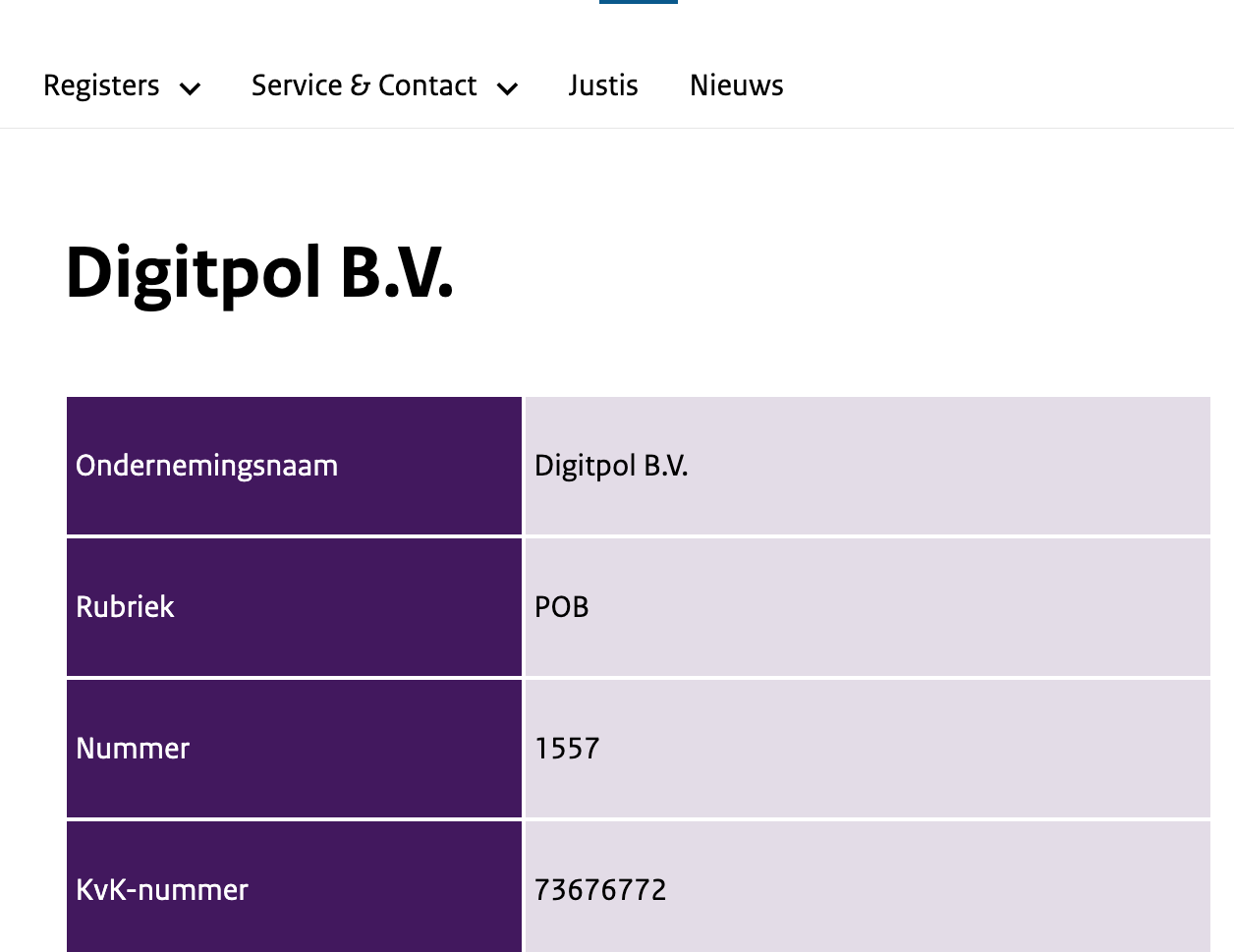
Digitpol’s computer forensics experts investigate, analyse and recover forensic data from computers, portable devices and hard disk drives. We ensure that no digital evidence is overlooked and assist at any stage of an investigation, regardless of the size or location of data sources. Claims of leaks, fraud, cyber espionage, financial tampering, computer crime, employee misconduct, and other illegal or wrongdoing actions require corporations, law firms, and government agencies to deploy digital forensic methods to piece together facts that lead to the truth.
Forensic examination of computers involves the systematic analysis of digital devices such as computers, smartphones, and other electronic storage devices to identify, preserve, and analyze potential evidence related to a digital crime or incident. It requires specialized knowledge and techniques to recover data from these devices in a forensically sound manner.
The forensic examination of computers involves several steps, including the identification of digital evidence, acquisition of the data, analysis of the data, and presentation of findings. The process must be conducted in a way that maintains the integrity of the data and ensures that the evidence is admissible in court.
During the examination, the forensic analyst looks for information such as deleted files, internet history, and email correspondence that can provide evidence of criminal activity. They may also look for metadata, which is data that provides information about other data. Metadata can provide important information, such as the date and time a file was created or modified, which can be used to establish a timeline of events.
Forensic examination of computers is a critical component of digital forensics investigations and is used in criminal investigations, civil litigation, and corporate investigations.